A Deep Dive Defensive Analysis
1. Introduction: A Defining Moment in Cyber Defense
In 2008, a seemingly simple infection vector—an infected USB drive—triggered one of the most consequential cybersecurity incidents in U.S. military history. The malware, later identified as Agent.btz, infiltrated classified and unclassified networks within the U.S. Department of Defense (DoD), forcing a fundamental reevaluation of how digital infrastructure is secured.
From a defensive standpoint, this was not just a breach—it was a systemic failure across multiple layers of security. It exposed gaps in endpoint visibility, policy enforcement, network architecture, and incident response maturity. The response effort, known as Operation Buckshot Yankee, became one of the largest coordinated cyber defense operations ever executed.
This analysis examines the incident through a blue team lens, focusing on defensive breakdowns, containment strategy, and the lasting architectural changes that followed.
2. The Security Landscape at the Time
The effectiveness of Agent.btz was not due to advanced sophistication. It succeeded because it entered an environment that was not designed to detect or contain it.
At the time, most organizations—including highly sensitive government environments—relied on:
- Signature-based antivirus
- Perimeter-focused defense models
- Implicit trust within internal networks
- Minimal control over removable media
- Limited telemetry from endpoints
Endpoint Detection and Response platforms were not widely deployed. Internal network monitoring was limited. Behavioral analytics were immature. Logging was inconsistent.
The prevailing model assumed that once inside the network, activity was largely trustworthy. This assumption proved catastrophic.
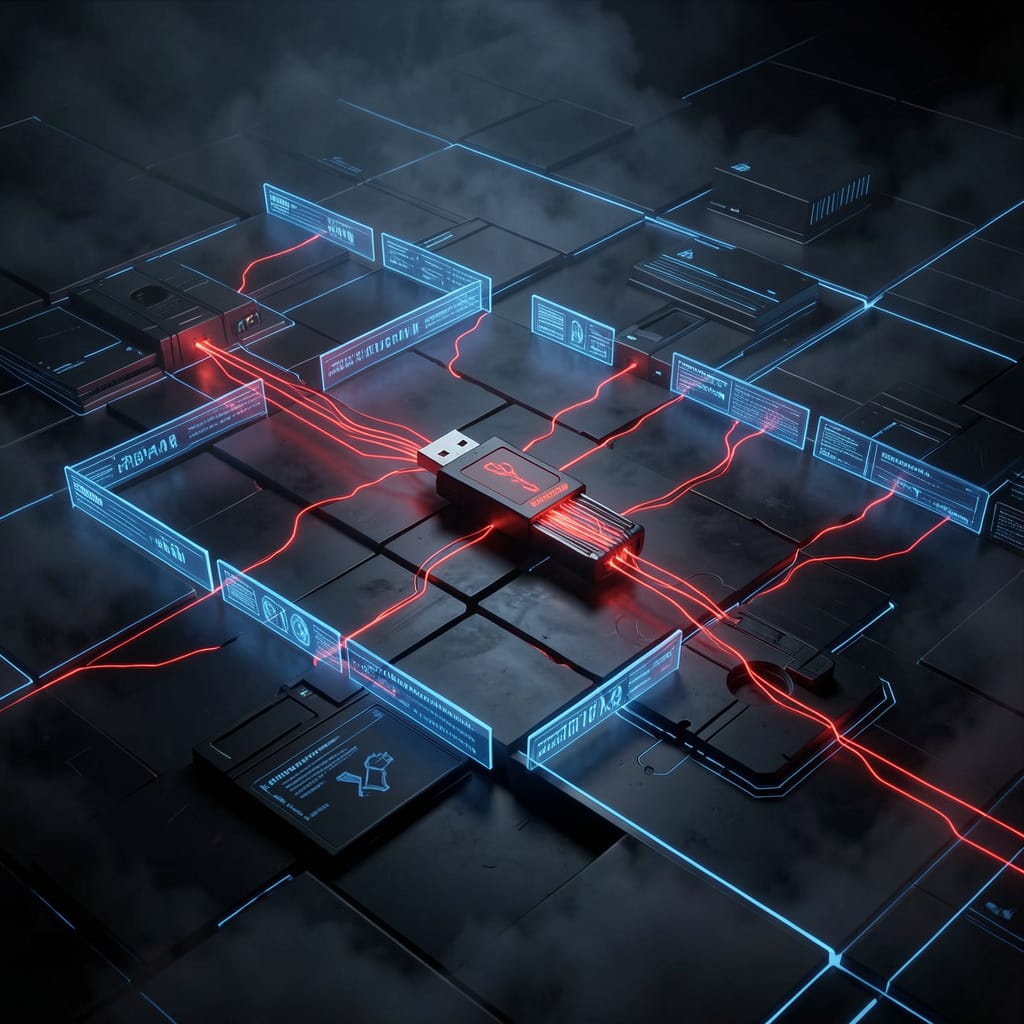
3. Initial Compromise: Removable Media as an Attack Vector
The initial infection occurred when a user inserted an infected USB device into a system connected to DoD networks. This completely bypassed traditional perimeter defenses.
There was no external exploit, no inbound attack, and no phishing vector. The compromise occurred through physical interaction with a trusted system.
The malware leveraged autorun functionality, which at the time was commonly enabled by default. This allowed execution without requiring meaningful user interaction or awareness.
From a defensive perspective, this highlights a fundamental issue:
The threat model did not account for trusted devices acting as delivery mechanisms for malicious code.
Any environment that assumes physical access equates to trust is inherently vulnerable.
4. Malware Behavior and Execution
Agent.btz was designed to spread and persist rather than perform highly targeted exploitation. Its effectiveness came from reliability and stealth within a permissive environment.
Key behaviors included:
- Replication to other removable media
- Establishment of persistence on infected systems
- Communication with external command-and-control infrastructure
- Basic data collection and exfiltration
- Use of common system processes to blend activity
The malware did not need to exploit zero-day vulnerabilities. It relied on:
- Weak internal controls
- Lack of monitoring
- Trust between systems
From a blue team standpoint, the lesson is clear: malware does not need to be advanced to be effective. It only needs to operate in an environment that lacks visibility and enforcement.
5. Internal Spread and Lateral Movement
Once inside the network, Agent.btz was able to propagate with minimal resistance.
The internal environment exhibited several weaknesses:
- Flat network architecture
- Limited segmentation between systems
- Over-permissive access controls
- Lack of internal firewall enforcement
- Minimal inspection of east-west traffic
This allowed the malware to move laterally, infect additional systems, and spread across both classified and unclassified environments.
The absence of internal trust boundaries enabled unrestricted movement. Systems trusted each other by default, and there were no meaningful controls to restrict that trust.
A properly segmented environment would have limited propagation and contained the blast radius.
6. Visibility and Detection Failures
One of the most significant failures in this incident was the inability to detect the compromise early.
Several factors contributed to this:
Lack of Endpoint Telemetry
There was no detailed logging of:
- Process creation
- Parent-child process relationships
- Execution from removable media
- File propagation patterns
Without this visibility, malicious activity blended into normal operations.
Dependence on Signature-Based Detection
Traditional antivirus solutions failed to identify the malware because:
- It was previously unknown
- It did not match existing signatures
- It used common execution techniques
This exposed the limitations of relying solely on known indicators.
Absence of Correlation and Analytics
Even if anomalies existed, there were no systems in place to correlate events across:
- Multiple endpoints
- Network activity
- User behavior
The result was a prolonged dwell time and widespread infection.
7. Response: Operation Buckshot Yankee
The response effort required coordination across multiple military branches and agencies. It was one of the largest cyber defense operations conducted by the United States.
Key actions included:
- Identification and isolation of infected systems
- Forensic analysis across networks
- Removal of unauthorized removable media
- Deployment of new monitoring capabilities
- Enforcement of strict security policies
One of the most impactful decisions was the immediate restriction of removable media across DoD environments. This was not a recommendation—it was enforced at scale.
The operation highlighted the need for centralized control, standardized procedures, and coordinated response mechanisms.
8. Core Defensive Lessons
Assume Breach
The incident demonstrated that perimeter defenses are not sufficient. Once an attacker gains access—through any vector—the internal environment must be capable of detecting and containing them.
Security strategy must begin with the assumption that compromise is inevitable.
Control Removable Media
Removable media represents a direct bypass of network-based controls. Defensive measures must include:
- Device control policies
- Whitelisting of authorized devices
- Full logging of usage
- Disabled autorun functionality
Without these controls, any endpoint becomes an entry point.
Require Endpoint Visibility
Detection depends on telemetry. Modern environments must capture:
- Process execution
- File activity
- Network connections
- Device interactions
Without this data, detection is guesswork.
Enforce Network Segmentation
Flat networks enable rapid propagation. Segmentation must be enforced through:
- VLAN separation
- Internal firewalls
- Access control lists
- Microsegmentation where possible
Each boundary reduces the attacker’s ability to move laterally.
Prioritize Behavioral Detection
Signature-based detection alone is insufficient. Detection must focus on:
- Unusual execution paths
- Abnormal file movement
- Unexpected network communication
- Deviations from baseline behavior
Unknown threats are the default, not the exception.
9. Policy and Governance Breakdown
The technical failures were compounded by weak policy enforcement.
Issues included:
- Lack of standardized controls across environments
- Inconsistent enforcement of security policies
- Absence of centralized oversight
- Delayed response coordination
Security policies that are not enforced have no value. Governance must ensure consistency, compliance, and accountability.
10. Evolution of Defensive Posture
The incident accelerated major changes in cybersecurity strategy within government environments.
These included:
- Increased investment in defensive capabilities
- Development of centralized cyber command structures
- Standardization of security practices
- Expansion of monitoring and detection capabilities
It marked a transition from reactive defense to structured, proactive security operations.
11. Mapping to Modern Attack Techniques
When analyzed using modern frameworks, the attack aligns with several known techniques:
- Replication through removable media
- Command and control communication
- Data exfiltration over application protocols
- Execution via scripting or system tools
Mapping historical incidents to current frameworks allows defenders to build relevant detection and response strategies.
12. Threat Hunting Opportunities
In a modern environment, this type of activity would generate multiple hunting opportunities:
- Detection of execution from removable media
- Identification of abnormal file replication patterns
- Correlation of device insertion with process activity
- Monitoring for unusual outbound connections
Effective threat hunting relies on both data availability and analytical capability.
13. Detection Engineering Considerations
Detection logic should focus on behaviors rather than signatures.
Key areas include:
- Execution from non-standard locations
- Rapid file propagation across systems
- Unauthorized external communications
- Correlation between user activity and system changes
Detection engineering must be continuous and adaptive.
14. Incident Response Maturity
Operation Buckshot Yankee exposed gaps in incident response processes.
Modern response frameworks now emphasize:
- Defined playbooks
- Rapid containment procedures
- Cross-team coordination
- Centralized communication
Response speed and coordination directly impact the scale of damage.
15. Modern-Day Relevance
The attack vector used in this incident remains relevant.
Similar patterns are observed in:
- Air-gapped environment compromises
- Supply chain attacks
- Insider threat scenarios
- Hardware-based attack vectors
The underlying issue—trust in uncontrolled inputs—has not changed.
16. Human Element
The initial compromise required a user action: inserting a device.
This reinforces that users are part of the security boundary. Training must focus on:
- Awareness of physical attack vectors
- Recognition of suspicious behavior
- Reporting procedures
Human behavior must be considered in all defensive models.
17. Building a Resilient Defense Model
A modern defensive architecture must operate across multiple layers:
Endpoint
- Advanced detection and response capabilities
- Application and device control
- Continuous monitoring
Network
- Segmentation and traffic inspection
- Internal visibility of east-west movement
- Detection of anomalous communication
Identity
- Strong authentication controls
- Monitoring of account behavior
- Enforcement of least privilege
Data
- Controlled access to sensitive information
- Monitoring of data movement
- Encryption and auditing
Each layer must function independently and collectively.
18. Automation and Response Efficiency
Manual response is too slow for modern threats. Automation must be integrated into defense operations.
Capabilities should include:
- Automatic isolation of compromised systems
- Real-time alert correlation
- Execution of predefined response actions
Reducing response time directly limits attacker effectiveness.
19. Strategic Takeaways
The incident reinforces several key points:
- Entry points will be missed
- Internal defenses must be strong
- Visibility determines detection capability
- Segmentation limits impact
- Policy enforcement is critical
- Automation enhances response
Failures in basic controls often lead to large-scale compromise.
20. Conclusion
Agent.btz and Operation Buckshot Yankee remain one of the most instructive case studies in defensive cybersecurity.
The attack did not rely on advanced techniques. It relied on gaps in visibility, enforcement, and architecture. Those same gaps continue to exist in many environments today.
The core lesson is not about the malware—it is about the environment that allowed it to succeed.
If a similar attack were introduced into a modern network, the outcome would depend entirely on whether these lessons have been implemented.
Security is not defined by the absence of threats. It is defined by the ability to detect, contain, and recover from them.






Leave a comment